Strengthening Cybersecurity: Enhancing Protection Through Virtualization Technology
04 Jul, 20228 minutesIn today's digital landscape, where data breaches and cyber threats loom large, businesses a...
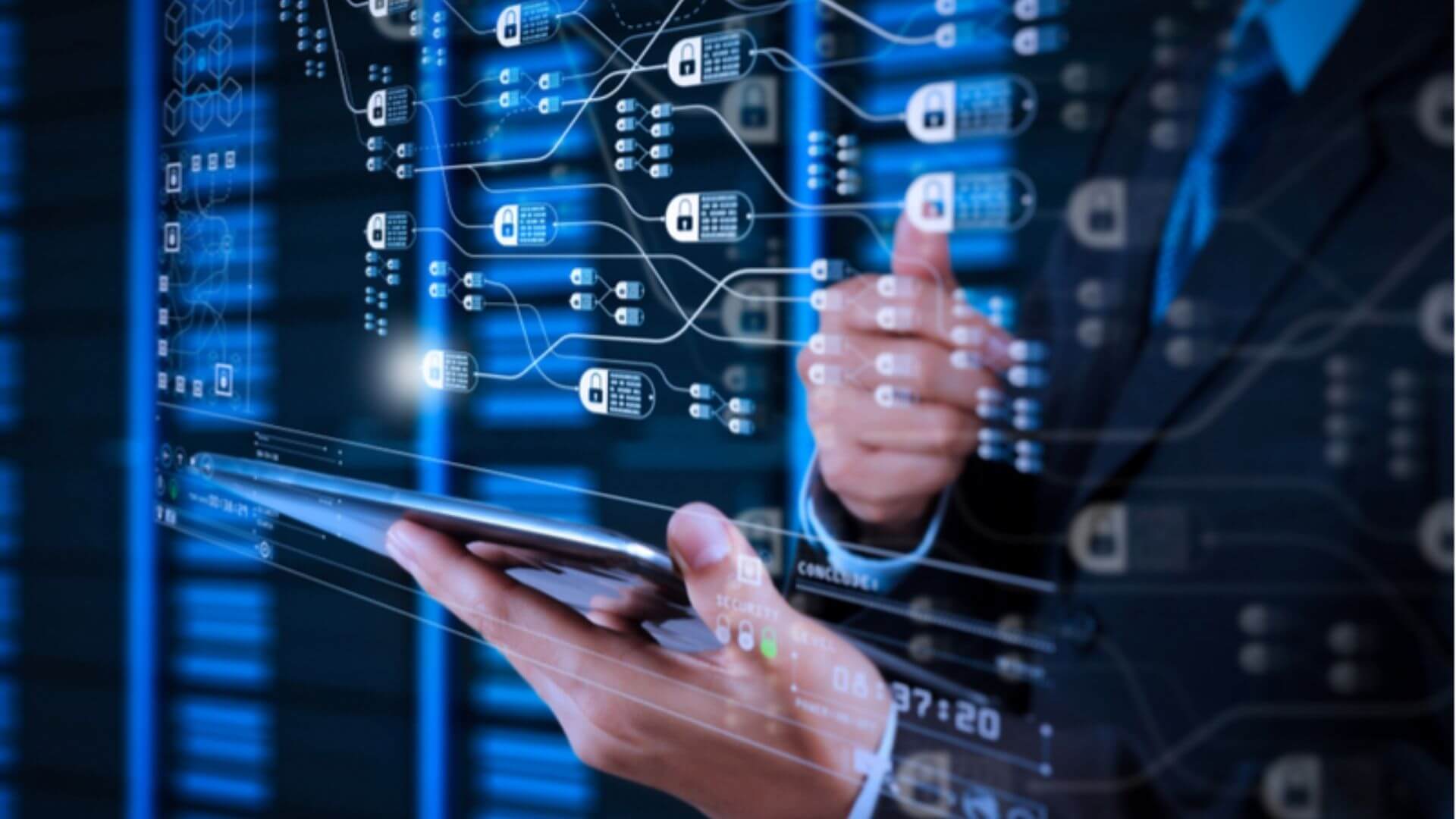
In today's digital landscape, where data breaches and cyber threats loom large, businesses are constantly seeking innovative ways to bolster their cybersecurity measures. Virtualization technology has emerged as a powerful tool in this endeavor, revolutionizing how organizations safeguard their sensitive information and digital assets. This article will explore virtualization technology, its advantages and disadvantages, and how it can enhance your business's cybersecurity.
We will delve into the following in this guide:
- What is virtualization?
- Cybersecurity solutions are a primary concern
- What are the advantages and disadvantages of virtualization?
- How virtualization technologies can enhance cybersecurity
What is virtualization?
Virtualization is the development of a virtual environment. It enables users to run different operating systems on the same computer. It creates a virtual, rather than physical, version of an operating system, a server, or network resources. Virtualization can be considered part of a broader trend in IT environments that will govern themselves based on recognized activity and utility computing in many organizations.
The most crucial objective of virtualization is to minimize administrative tasks while improving scalability and workloads. However, virtualization can also be used to improve security.
In today's work context, virtualization offers numerous advantages. Running many workloads allows physical server resources to reach their full potential. Operating system instances can be divorced from the underlying hardware and move freely between several hosts in a cluster setup without causing any negative consequences.
High-availability mechanisms that were never before possible, such as the ability to restart virtual machines (VM) on a separate server if the primary host dies, are now possible. By abstracting the network from the underlying physical network switches, wiring, and other devices, virtualized networking provides many of the same benefits to network traffic.
But why has virtualization grown to such prominent importance? Scroll to our next section to find out.
Cybersecurity solutions are a primary concern
Organizations today are quickly recognizing how critical cybersecurity objectives are, regardless of the project or business activities involved. However, security is being scrutinized more than ever before, particularly concerning technology and IT infrastructure.
Large-scale, high-profile data breaches that make significant news headlines are not the type of attention companies want. Ransomware attacks that disrupt business-critical systems are equally alarming. Today's businesses must have a razor-sharp focus on security concerns and how to effectively address them.
Security cannot be an afterthought with any plans to integrate new technologies or go forward with the latest infrastructure. It must be built into the project as a required component to ensure that essential aspects of the security thought process are not overlooked. The virtualization era has altered the way businesses think about security and privacy. Many security boundaries in the strictly physical world have been broken down because of virtualized technology.
After installing new technology, many companies consider security concerns as a high priority. Fortunately, virtualization has numerous advantages, making it simple to sell in IT architectures. Virtualization can help you save money, improve business efficiency, reduce maintenance downtime without disrupting operations, and get more work done with less equipment. In our next point, let's outline the key advantages and disadvantages of virtualization in cybersecurity.
What are the advantages and disadvantages of virtualization?
Virtualization technology presents a double-edged sword in cybersecurity, offering advantages and disadvantages as a virtual partner to your business. On the positive side, virtualization enhances security through isolation, streamlined patch management, and disaster recovery capabilities. However, it also introduces potential vulnerabilities through hypervisor security, the risk of VM sprawl, and resource sharing.
In this section, we will underline the pros and cons of virtualization in the context of cybersecurity to help you make informed decisions about its implementation into your business.
Advantages of virtualization technology in cybersecurity
There are various advantages of virtualization technology in cybersecurity, which are all highly impactful. This section highlights these benefits and how virtualization enhances security measures, such as isolation, testing and analysis, efficient patch management, disaster recovery, and reducing the hardware footprint. Collectively, these advantages can strengthen your organization's ability to safeguard its digital assets and maintain operational continuity.
Let’s explore these advantages of virtualization technology in cybersecurity:
- Isolation and Segmentation: Virtualization provides a robust mechanism to isolate applications and workloads. Each VM functions within its dedicated environment, creating a barrier that prevents the spread of malware or cyberattacks from one VM to another. In the event of a breach, the impact can be contained, limiting the potential damage and reducing the attack surface.
- Enhanced Testing and Analysis: Virtualization facilitates the creation of sandbox environments for testing and analyzing potentially harmful software or files. Security teams can dissect suspicious code or applications within isolated VMs, ensuring the primary system remains untouched. This proactive approach allows organizations to identify and neutralize threats before they infiltrate the network.
- Efficient Patch Management: Virtualization technology streamlines the application of security patches and updates. IT administrators can create snapshots of VMs before implementing patches. If a patch causes compatibility issues or vulnerabilities, the VM can be instantly reverted to its previous state, mitigating the risk of disrupting critical operations.
- Disaster Recovery and Business Continuity: Virtualization contributes to robust disaster recovery strategies. VMs can be replicated and stored in off-site locations, allowing for a swift recovery in case of a cyber incident or system failure. The ability to restore the entire virtual environment expedites business continuity efforts, minimizing downtime and data loss.
- Reduced Hardware Footprint: Virtualization's ability to consolidate multiple VMs onto a single physical server reduces the hardware footprint. This advantage not only leads to cost savings but also simplifies security management by providing a centralized platform for monitoring and securing VMs.
Disadvantages of virtualization technology in cybersecurity
Compared to the advantages, the disadvantages of virtualization technology in cybersecurity are few and far between. While virtualization technology offers substantial cybersecurity benefits, addressing its disadvantages is also essential.
Here are the disadvantages of virtualization technology in cybersecurity:
- Hypervisor Vulnerabilities: The hypervisor manages multiple VMs on a host server and must be meticulously secured to prevent unauthorized access. Any compromise to the hypervisor could lead to a breach of all hosted VMs.
- VM Sprawl: Poor management of VMs can result in VM sprawl, where unused or outdated instances continue to exist. This can create security gaps and increase the attack surface.
- Shared Resources: Overloading a physical server with too many VMs can lead to resource contention, impacting performance and potentially creating vulnerabilities.
Summarizing this section, it’s clear that virtualization technologies play a pivotal role in bolstering cybersecurity defenses, offering a range of advantages that include isolation, efficient testing, patch management, disaster recovery, and resource optimization. By harnessing the power of virtualization, organizations can create a more resilient and adaptable security infrastructure.
However, despite the pros outweighing the cons, it’s imperative to remain vigilant against the inherent disadvantages of virtualization, such as hypervisor vulnerabilities, the potential for VM sprawl, and resource-sharing challenges.
As the cybersecurity landscape evolves, a balanced approach that maximizes the advantages while mitigating the disadvantages is crucial to maintaining a robust and secure digital environment. Ultimately, the success of virtualization in cybersecurity hinges on strict management, constant monitoring, and a commitment to staying one step ahead of emerging threats.
To keep one step ahead of these threats and minimize risks to improve your security through virtualization, scroll to our final section on how virtualization technologies can enhance cybersecurity.
How virtualization technologies can enhance cybersecurity
As we’ve established, virtualization technologies have emerged as a formidable ally in the world of cybersecurity, offering innovative strategies to minimize risk and counter the most common cybersecurity threats. In this section, we’ll delve into how virtualization can be harnessed to bolster security measures.
From the practicality of sandboxing to the resource optimization of server virtualization and the enhanced network security and segmentation brought about by network virtualization to the user-centric security advantages of desktop virtualization, these techniques collectively provide a versatile toolkit for safeguarding digital environments against evolving cyber threats.
Sandboxing
Sandboxing is a security strategy that isolates running applications from untrusted third parties, vendors, and websites. It's commonly used to run untested code or programs. Sandboxing's primary purpose is to increase virtualization security by isolating an application to protect it from external malware, destructive viruses, and stopped-running apps, among other things. Put any experimental or unstable apps in a virtual machine. The remainder of the system is unaffected.
Since your application can be maliciously attacked while running in a browser, running your apps on a virtual machine is always a good idea. Virtualization and sandbox technology are closely related. Virtual computing provides some of the advantages of sandboxes without the high cost of a new device. The VM is connected to the Internet rather than the corporate LAN, which protects the operating system and apps from viruses and other malicious threats.
Server Virtualization
Server virtualization involves the process of dividing physical servers into smaller virtual servers to maximize resources. The physical servers are divided into many virtual environments by the administrator. Hackers nowadays frequently steal official server logs. Small virtual servers can run their own operating systems and restart independently thanks to server virtualization. Stable and compromised programs are identified and isolated using virtualized servers.
This sort of virtualization is most commonly found on web servers that offer low-cost web hosting. Server utilization manages the complex aspects of server resources while enhancing utilization and capacity. Furthermore, a virtualized server makes detecting dangerous viruses or other harmful items simple whilst safeguarding the server, virtual machines, and the entire network.
Network Virtualization
Network virtualization combines network hardware and software resources, as well as network functionality, into a single virtual network. Virtual networks, which use network virtualization, reduce the impact of malware on the system. Furthermore, network virtualization produces logical virtual networks from the underlying network hardware, allowing virtual environments to better integrate.
Isolation is an essential feature of network virtualization. It allows end-to-end custom services to be implemented on the fly by dynamically combining various virtual networks that coexist in isolation. They share and utilize network resources received from infrastructure providers to operate those virtual networks for users.
Segmentation is another crucial element of network virtualization. The network is divided into subnets, improving performance by reducing local web traffic and enhancing security by making the internal network structure invisible from the outside. Network virtualization is also utilized to develop a virtualized infrastructure to fulfill complicated requirements by generating single instances of software programs that serve many customers.
Desktop Virtualization
This lets users generate, change, and delete photos while also separating the desktop environment from the computer that is used to access it. Administrators may simply manage employee computers with desktop virtualization. This protects people from attacking computers with viruses or gaining illegal access.
Additionally, the user gains additional security from the guest OS image for the desktop environment. Such an environment allows the users to save or copy data to the server rather than the disk, thus making desktop virtualization a more secure option for networking.
The final word on cybersecurity virtualization technology
On the security front, virtualization is possibly one of the most sufficient strategies businesses can use to combat harm and criminal intent. These principles demonstrate how virtualization can help your firm reduce risk and increase security.
Regular upgrades and vulnerability scans are required for all technology-based systems, virtualization included, to reduce the chance of weakness. Adopting hardened virtual machine images is strongly recommended.
Of course, to fully embrace how virtualization technology can be your cybersecurity solution, you need cybersecurity specialists who can implement it into your business for you. Thankfully, finding these people is something you don't have to do alone. Scroll below to find out more.
Looking for cybersecurity recruitment specialists?
Are you looking to improve your cybersecurity structure by introducing virtualization into your business but need help figuring out where to start? We can help. Our team of cybersecurity recruitment specialists will act as your partner to identify and connect you with top-tier candidates in the market. These individuals possess the capabilities to steer your business toward sustained success and virtualization technology.
Contact us today to discuss your cybersecurity recruitment needs and discover how we can provide you with the best talent to drive long-term success for your organization.